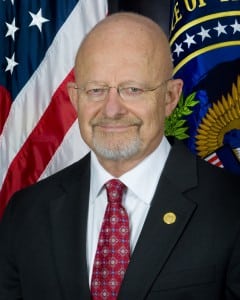
James Clapper, Director of National Intelligence (DNI), reiterated on Tuesday that cybersecurity is the top national threat in hearings on the Intelligence Community’s (IC) Worldwide Threat Assessment.“The consequences of innovation and increased reliance on information technology in the next few years on both our society’s way of life in general and how we in the Intelligence Community specifically perform our mission will probably be far greater in scope and impact than ever,” Clapper said in a written statement at hearings…

 By
By 










