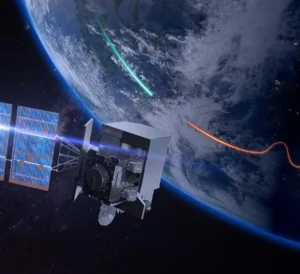
Northrop Grumman’s [NOC] cybersecurity strategy has focused on embedding cyber protections into its products during their development phases, company officials said yesterday. “The value of embedded cyber means that it allows our customers to cyber harden their platforms up front by building in good systems engineering, good architectural approaches and designing cyber in from the very start,” said Mike Papay, Northrop vice president and chief information security officer, at a briefing on Tuesday. The company said the strategy increases efficiency…
Recommended
Trending
Congress Updates
Appropriators Press For Details On Iran War Costs; DoD’s $29B Estimate Doesn’t Include Base Damage
The Pentagon estimates the U.S.’ ongoing conflict with Iran has now cost at least $29 billion, while a lead official noted the updated figure does not factor in damage to […]
Appropriators Offer Skepticism On $350B Defense Reconciliation Plan, ‘Big Risk’ For Key Initiatives
Senate and House Appropriators told Pentagon leadership on Tuesday they’re skeptical of the department’s plan to fund $350 billion of the fiscal year 2027 defense budget through the reconciliation process, […]
All Future Systems Should Have Autonomy Features, Reed Says
Last week, Sen. Jack Reed (D-R.I.) visited North Kingstown, R.I.-based Senesco, which is teaming with autonomous systems company Havoc to bid on the U.S. Navy’s Medium Unmanned Surface Vessel program. […]
Senate Appropriators Concerned With DoD’s Reconciliation Plan For Top FY ‘27 Priorities, Aide Says
Senate defense appropriators have concerns with the Pentagon’s decision to include key fiscal year 2027 funding priorities, such as critical munitions and drones production, among its request for $350 billion […]
Job Feed
-
Model Based Systems Engineer (MBSE) Modeler (ES1)
St. Louis, MO - Epsilon Systems Solutions, Inc - St. Louis, MO -
Sales Manager, Regional
COMTECH TELECOMMUNICATIONS - Los Angeles, CA -
Sr. Threat Hunting Intelligence Analyst (Remote, East/Central)
CrowdStrike, Inc. - Arlington, VA -
Sales Manager, Regional
COMTECH TELECOMMUNICATIONS - Orlando, FL