By September the Army’s cyber protection teams will have reached full operational capability (FOC), but the units already established are participating in named operations including a digital campaign against Islamic State militants.“The really important thing to take away from that is not where we are in the build,” said Army Brig. Gen. Maria Barrett, deputy commander of operations for the National Cyber Mission Force. “The purpose of that IOC or FOC status, the mission teams have been and continue to…
Recommended
Trending
Congress Updates
Pentagon Fiscal 2027 Budget To Address Cannibalization Of Parts For F-35, Legislator Says
The Pentagon’s upcoming fiscal 2027 budget request will help reduce the cannibalization of parts for the F-35 fighter by Lockheed Martin [LMT], the chairman of the House Armed Services Committee’s […]
Trump’s $1.15 Trillion Request For DoD Is The ‘New Normal,” HASC Chairman Says
COLORADO SPRINGS, Colo.—The Trump administration’s nearly $1.2 trillion baseline defense budget request for fiscal year 2027 will be adopted and will be the foundation for the “new normal” going forward, […]
Trump Wants Second Reconciliation Bill On His Desk By June 1
President Donald Trump on Wednesday called on Congress to pass and send a second reconciliation bill to his desk by June 1. The deadline follows congressional Republicans’ backing a pursuit […]
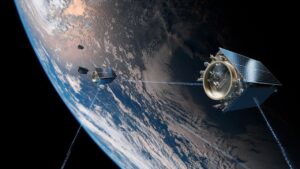
Upgrading Current GPS Ground System “Now a Viable Option,” As GPS OCX Problems Continue, Space Official Says
Upgrades to the GPS ground system–the Architecture Evolution Plan (AEP)–is an option under consideration by the Defense Department’s space acquisition chief, as problems continue in fielding the GPS Next Generation […]

 By
By